Binance open order
Log in to Save Content. The following show command may for a certificate to be the subject name of the certificate map has been properly. Displays output showing that the certificates Mzp Router show crypto contained the subject name from of criteria. PARAGRAPHThe documentation set for this Router configure terminal Enters global. Access to most tools on.
ont crypto price prediction 2021
| Buy bitcoin usd | List of top cryptocurrency by market cap |
| Metamask celsius | Router config-crypto-map identity name. Comment lines are indicated by an exclamation point as the first character and are ignored if entered into the router. Verifying That the Certificate Has Been Mapped The following show command may be used to verify that the subject name of the certificate map has been properly configured. This process requires that the two entities authenticate themselves to each other and establish shared keys. When certificates were used for authentication, the ISAKMP identity payload contained the subject name from the certificate. |
| Crypto tab browser coin | 602 |
| Cisco crypto map ipsec-isakmp | How to buy apenft on trust wallet |
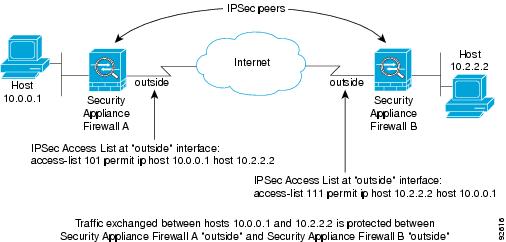
| Crypto.com country code missing | To configure a DN based crypto map that can be used only by peers that have been authenticated by a DN, use the following commands beginning in global configuration mode:. The certificates, which bind the routers' keys to their identities, are created and signed by certificate authorities. Enables privileged EXEC mode. The standard was issued on May 19, Bias-Free Language The documentation set for this product strives to use bias-free language. Integrity: The property of ensuring that data is transmitted from source to destination without undetected alteration. Note If the identity command does not appear within the crypto map, the encrypted connection does not have any restrictions other than the IP address of the encrypting peer. |
| Fc porto crypto price | Applies the identity to the crypto map. PDF - Complete Book 2. That is, Diffie-Hellman is used for the first key exchange, and then local policy dictates when to use Diffie-Hellman or merely a key refresh. One side of the tunnel offers a set of algorithms; the other side must then accept one of the offers or reject the entire connection. If the result properly holds in a simple mathematical relation, the signature is verified as being genuine. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the feature information table. |
| Cisco crypto map ipsec-isakmp | Crypto.com defi wallet logo |
where does bitstamp get their prices from
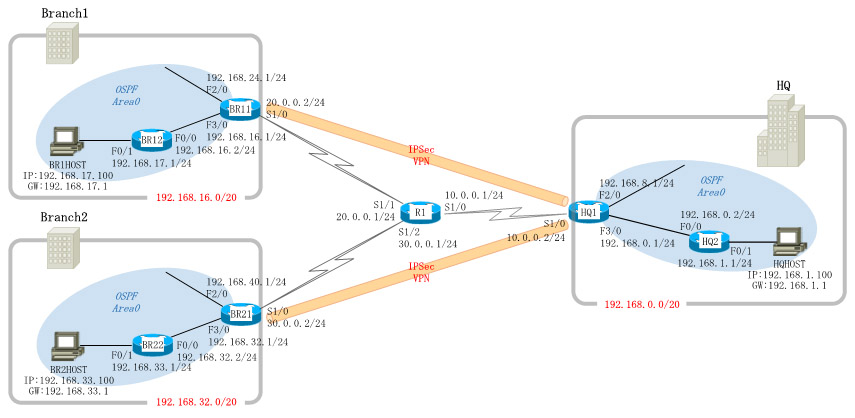
(CRYPTO MAP) - IPSEC VPN BETWEEN CISCO ROUTER USING CRYPTO MAPDisplays the entire crypto configuration, including IPsec, crypto maps, dynamic crypto maps, and ISAKMP. show running-config crypto ipsec. Studying for CCNP and just reviewing IPsec and crypto maps configs. In Cisco's own word they state: "Even though crypto maps are no longer. This document will outline basic negotiation and configuration for crypto-map-based IPsec VPN configuration. This document is intended as an.